When employees of the U.S.-based pharmaceutical giant Merck arrived at their offices the morning of June 27th, 2017, they were greeted with a disturbing message upon turning on their computers. PCs throughout the company had been hacked and critical files locked up via encryption, with the hackers promising to release the files for $300 in bitcoin per affected computer.
What has since been dubbed the NotPetya cyberattack was not just limited to Merck – companies around the world and government ministries in Ukraine were also affected. Merck was particularly hard hit, however. The morning of the attack, the company was forced to disable its email system and prohibit its 70,000 employees from touching their computers. After a few hours of confusion, all employees were sent home. All told, the ransomware attack impacted Merck’s global manufacturing, research and sales productivity for nearly a week and cost the company an estimated $310 million dollars in the third quarter of 2017 due to increased operating expenses and lost sales.
Healthcare cybersecurity is a mounting concern. As reported by the HIPAA Journal, other than 2015, healthcare data breaches have increased every year since the Department of Health and Human Services’ Office for Civil Rights began tracking breach data in October 2009. 2019 showed a marked increase in data breaches, with 510 healthcare data breaches of 500 or more records being reported, representing a 196% increase from 2018.
With increasing connectivity of computer-workstations, mobile devices, information systems and laboratory instruments, the attack surface is growing, and hackers are developing more sophisticated tools and techniques to gain access to important data. In addition, the remote work revolution ushered in by COVID-19 has stretched organizational digital boundaries significantly, making good cybersecurity practices even more imperative.
While large pharmaceutical companies are an enticing target for hackers, with large quantities of research, clinical trial, patient data, and intellectual property (IP) to protect, these organizations typically have the funds to invest in good cybersecurity systems and practices. Research collaborators (e.g., Universities, research hospitals, teaching hospitals, etc.) that have access to a pharmaceutical company’s data, but may not have the same strict security protocols in place, provide the easiest target for hackers. Hackers look for the weak points in a network, and there can be notable cybersecurity gaps in the areas of clinical and research data for many of these smaller collaborators in the pharma research ecosystem.
The life science industry has a need for a cybersecurity standard that serves to facilitate secure and productive collaboration in health research. In this blog, we will propose a risk-based security framework to fulfill this need based on the model used by the grant issuing agency of the NIH. This model is cost-effective and allows research organizations to maintain high levels of productivity.
Federal Cybersecurity Standards
Pharmaceutical companies seek to create a research ecosystem that is both productive and secure utilizing a variety of different collaborators. When sharing research data with a collaborator, they need assurance that the partner has an acceptable level of security practices to protect sensitive research data both in transit and when it arrives at its destination.
In the payments industry, PCI DSS compliance is mandated by credit card companies to ensure the security of credit card transactions. Unfortunately, there is no official security standard in the life science industry that would serve to expedite the assessment of potential research partners for pharmaceutical companies. As a result, pharma companies will often send a massive 300-question survey to a potential collaborator to assess their security practices before moving forward with data sharing. For obvious reasons, this evaluation method is cumbersome, time-consuming, and subjective.
A proposed solution to this problem is to apply federal cybersecurity standards that are well documented and can be tailored to fit the pharmaceutical research ecosystem. In 2002, the Federal Information Security Management Act (FISMA) was signed into law. The FISMA objective was to define the appropriate extent of security controls and measures commensurate with the risk and potential damage done by the unauthorized use, destruction, theft, or sequestering of federal agency data. This act gave National Institutes of Standards and Technology (NIST) the ability to set security requirements to ensure the safe harbor and transfer of protected federal information.
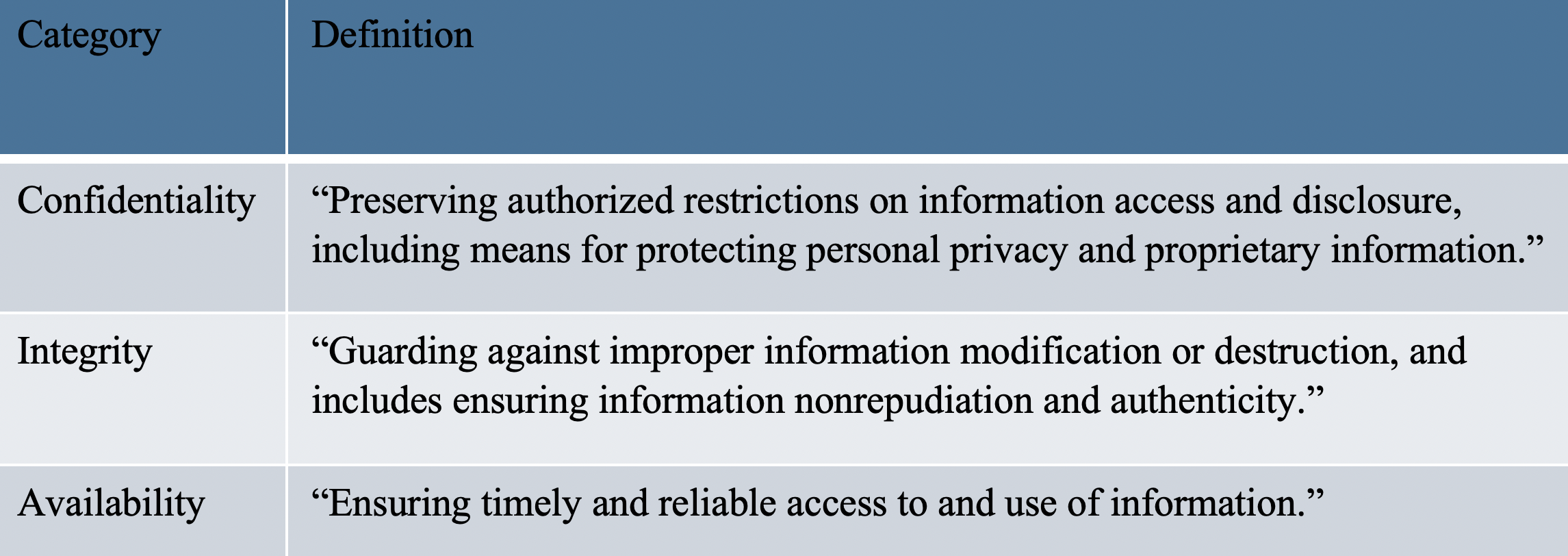
The risk-based, flexible approach of the NIST framework makes it particularly well-suited for a research environment. The NIST security requirements apply to all branches of the military and federal agencies, including the grant issuing agency of the NIH. The requirements are implemented to ensure the security of information in the following categories:
- Confidentiality
- Integrity
- Availability
The NIST Risk Management Framework (RMF)
In a typical research ecosystem, there is a central research IT group that effectively functions as a managed service provider for many different collaborating labs, all of which have different data security needs based on the type of work they are doing and the data they are handling. A collaborator’s risk profile can range from very low (e.g., doing research on low risk or model organisms) all the way up to high (e.g., clinical research where you are handling genetic profiles of patients).
It doesn’t make sense from a cost or operational perspective for the central research IT group to apply the same stringent security standards to everyone in the network. They simply don’t have the capability to manage and/or embed resources in every single lab or collaborator that needs to be managed. What the managing IT group needs is a risk-based template that enables them to manage security for a variety of systems effectively under one roof with very few people.
From the scientist’s perspective, those doing low risk discovery activities want to maximize data sharing and collaboration, and don’t want or need to be burdened with stringent security checklists that slow down their research. A risk-based approach to data security also benefits the researchers, as it is tailored to their individual data protection needs. This makes researchers happier, as they are getting the security level they need without hampering innovation.
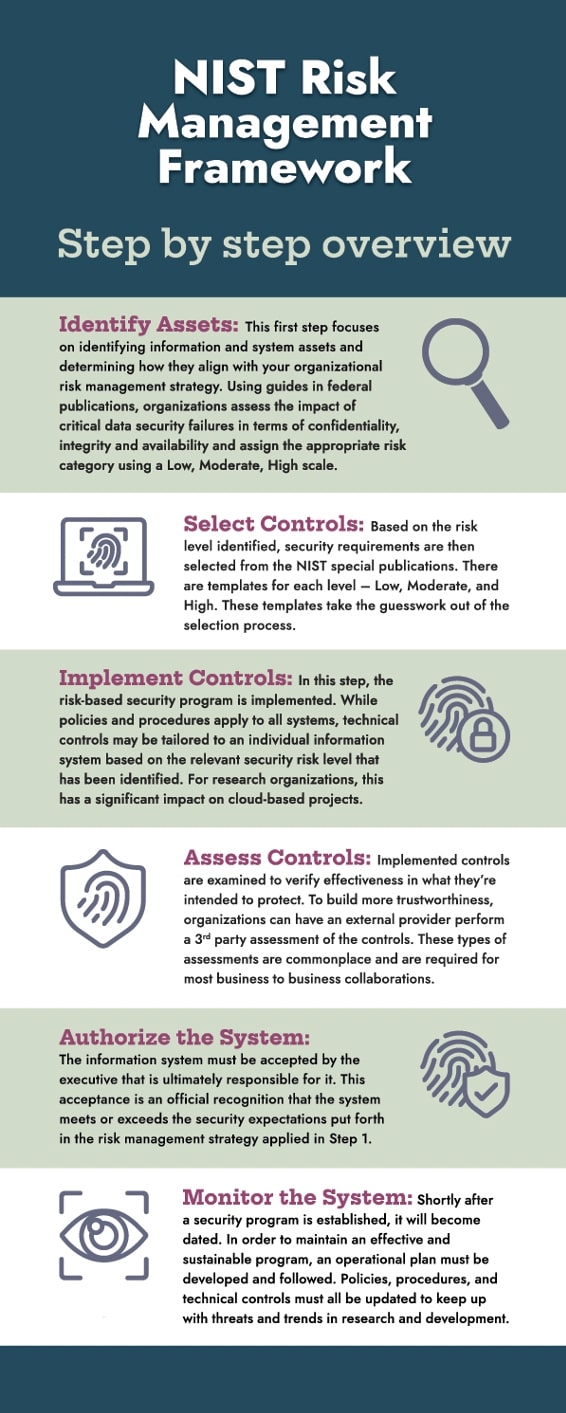
To address these needs in the context of FISMA, NIST developed a 6-step process called the Risk Management Framework (RMF). The grant issuing agency of the NIH uses this framework to manage security for the many different institutes and constituents that they work with, and they DO NOT require a large security team to manage the program. The RMF is tailored to meet the requirements of confidentiality, integrity, and availability (CIA) based on the assessed risk of each organization in the network.
The NIST RMF provides a comprehensive data security template that could be applied to a pharmaceutical research ecosystem. That said, organizations within the ecosystem would not follow RMF exactly as it is written. The idea here is to use the RMF as a template, while aspiring to not stray too far from it.
An infographic which gives a brief overview of the RMF follows:
Customized Security Plans for Pharmaceutical Companies and Collaborators
While some organizations in the pharma research ecosystem may want to pursue a comprehensive RMF approach, which can include NIST audits and internal certification, others may have less aggressive goals. It is important to work with a third party consultant who understands the RMF template but can also create a customizable security program based on the customer’s objectives.
For example, an organization that is interested in becoming a more attractive and/or trustworthy partner for a pharmaceutical sponsor or a grant issuing agency like the NIH may be interested in adopting the Risk Management Framework. Some collaborators may be interested in an RMF program only for high-risk systems, while others may build a program for the entire organization. On the other hand, an organization that is simply interested in shoring up the security of operations may just want to increase researcher awareness of the security systems in place with a comprehensive training program.
By employing a risk-based methodology, along with the right processes and technologies, organizations can secure their research data and maintain a high-level of productivity in their discovery activities to fuel innovation. A quality security consultant is focused on helping research IT organizations and their collaborators have a better understanding and control of their environment, along with a more directed and informed investment of resources, through a customizable security plan that is based on the client’s goals.
Benefits of Cybersecurity for Research Data
A quality cybersecurity program provides a number of important benefits for research organizations. A few of these include:
- For collaborators pursuing NIST certification, it establishes a level of trustworthiness that sets the organization apart.
- The process of filling out a 300-question survey from a pharmaceutical company is easy and painless, as all your policies and procedures are well documented.
- Keeps researchers happy, as they get a security checklist that is appropriate for the data they are working with.
- Allows managers to allocate resources more intelligently based on the system risk profile.
- Helps to establish effective collaboration between research and security professionals by improving education and awareness.
- Helps to strengthen and mature business practices.
- Helps to maintain strong partnerships.
- Improves operational efficiency and security.
Conclusion
Scientific discovery in the life sciences is a highly data-driven and collaborative process. As such, facilitating secure and productive data sharing in health research is essential to fuel the innovation pipeline. Yet as industry-leading pharmaceutical organizations strive to integrate legacy systems and digitize all aspects of the product lifecycle in order to gain a competitive edge, the need to continuously protect all forms of data in all locations and transmissions can become a challenging task.
Researchers want full control of their data to enhance their research through collaborations with colleagues and organizations. Security teams, on the other hand, have the challenge of protecting information from unauthorized use and disclosure. On the surface, these two perspectives seem at odds with one another, and yet most businesses must be able to provide information to partners and services.
In practice, the interface between research and security within life science organizations is often plagued with dysfunction. We attribute the root of this dysfunction to gaps in communication and understanding between the two groups, along with complex data protection needs. To overcome this challenge, it is possible to leverage a facilitating security consultant that is fluent in the languages and needs of researchers, research technologies, and cybersecurity. A quality security consultant can bridge the gaps between these groups and establish a manageable cybersecurity program that is effective, comprehensible, and complimentary to the field of research and development.
In this blog, we described a risk-based cybersecurity framework for the life science industry that that aligns with federal grant agencies and is tailored to support the needs of researchers. Whether applied to a single system or a multi-cloud environment, the program scales as needed, is cost-effective, can be managed by a small team, and serves to facilitate secure and productive collaboration in health research. This model allows research organizations to maintain high levels of productivity, ultimately helping to facilitate the innovative research that delivers life-changing medications to patients in need.



